CCNA Cybersecurity Operations (Vesion 1.1) – CyberOps Chapter 4 Exam Answers
- If the default gateway is configured incorrectly on the host, what is the impact on communications?
- The host is unable to communicate on the local network.
- There is no impact on communications.
- The host can communicate with other hosts on remote networks, but is unable to communicate with hosts on the local network.
- The host can communicate with other hosts on the local network, but isunable to communicate with hosts on remote networks. *
- Which message delivery option is used when all devices need to receive the same message simultaneously?
- Duplex
- Unicast
- Multicast
- Broadcast *
- How is a DHCPDISCOVER transmitted on a network to reach a DHCP server?
- A DHCPDISCOVER message is sent with a multicast IP address that all DHCP servers listen to as the destination address.
- A DHCPDISCOVER message is sent with the broadcast IP address as the destination address.
- A DHCPDISCOVER message is sent with the IP address of the default gateway as the destination address.
- A DHCPDISCOVER message is sent with the IP address of the DHCP server as the destination address.
- What part of the URL, http://www.cisco.com/index.html, represents the top-level DNS domain?
- www
- http
- index
- com
- The graphic shows a network diagram as follows:
PC A connects to switch S1, which connects to the G0/0 interface of router R1. PC B connects to switch S2, which connects to the G0/1 interface of router R1. A network analyst is connected to switch S2. The address of each device is as follows:
PC A: 192.168.1.212 and FE80::1243:FEFE:8A43:2122 and 01-90-C0-E4-55-BB
PC B: 192.168.2.101 and FE80::FBB2:E77A:D143 and 08-CB-8A-5C-D5-8A
R1 G0/0:192.168.1.1 and FE80::1 and 00-D0-D3-BE-79-26
R1 G0/1: 192.168.2.1 and FE80::1 and 00-60-0F-B1-D1-11
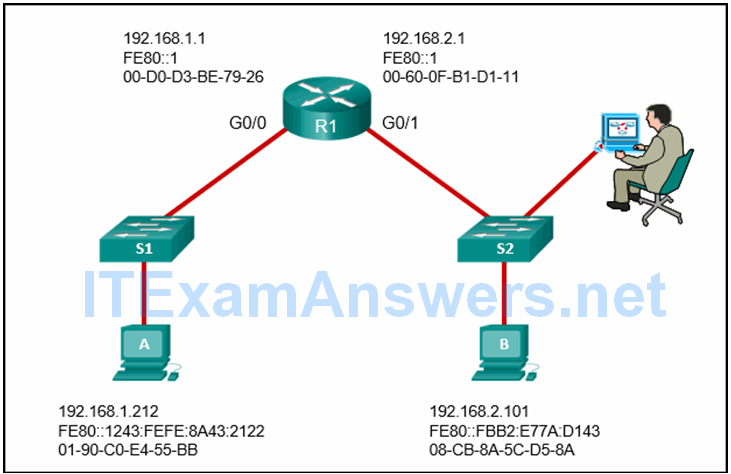
Refer to the exhibit. A cybersecurity analyst is viewing captured ICMP echo request packets sent from host A to host B on switch S2. What is the source MAC address of Ethernet frames carrying the ICMP echo request packets?
- 08-CB-8A-5C-D5-BA
- 00-D0-D3-BE-79-26
- 00-60-0F-B1-D1-11
- 01-90-C0-E4-55-BB
- Refer to the exhibit. A cybersecurity analyst is viewing captured packets forwarded on switch S1. Which device has the MAC address 50:6a:03:96:71:22?
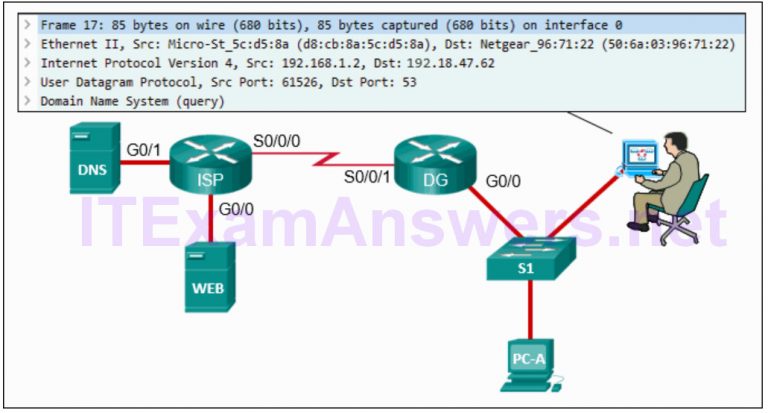
- PC-A
- router DG
- DSN server
- router ISP
- web server
Explanation: The Wireshark capture is of a DNS query from PC-A to the DNS server. Because the DNS server is on a remote network, the PC will send the query to the default gateway router, router DG, using the MAC address of the router G0/0 interface on the router. - Which term is used to describe the process of placing one message format inside another message format?
- encoding
- multiplexing
- encapsulation
- segmentation
- Which PDU format is used when bits are received from the network medium by the NIC of a host?
- frame
- file
- packet
- segment
- What addresses are mapped by ARP?
- Destination IPv4 address to the source MAC address
- Destination IPv4 address to the destination hostname
- Destination MAC address to the source IPv4 address
- Destination MAC address to a destination IPv4 address *
- Which statement is true about FTP?
- The client can download data from or upload data to the server. *
- The client can choose if FTP is going to establish one or two connections with the server.
- FTP is a peer-to-peer application.
- FTP does not provide reliability during data transmission.
- Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
- Session
- Transport *
- Network *
- Data link
- Physical
- Which statement is true about the TCP/IP and OSI models?
- The TCP/IP transport layer and OSI Layer 4 provide similar services and functions. *
- The TCP/IP network access layer has similar functions to the OSI network layer.
- The OSI Layer 7 and the TCP/IP application layer provide identical functions.
- The first three OSI layers describe general services that are also provided by the TCP/IP Internet layer.
- Which application layer protocol uses message types such as GET, PUT, and POST?
- SMTP
- POP3
- DHCP
- HTTP
- DNS
- Which transport layer feature is used to guarantee session establishment?
- UDP sequence number
- TCP 3-way handshake
- TCP port number
- UDP ACK flag
- What is the prefix length notation for the subnet mask 255.255.255.224?
- /26
- /27
- /28
- /25
- What are two potential network problems that can result from ARP operation? (Choose two.)
- Multiple ARP replies result in the switch MAC address table containing entries that match the MAC addresses of hosts that are connected to the relevant switch port.
- Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent of intercepting network traffic.
- On large networks with low bandwidth, multiple ARP broadcasts could cause data communication delays.
- Manually configuring static ARP associations could facilitate ARP poisoning or MAC address spoofing.
- Large numbers of ARP request broadcasts could cause the host MAC address table to overflow and prevent the host from communicating on the network.
- Which TCP mechanism is used to identify missing segments?
- sequence numbers
- FCS
- acknowledgments
- window size
- What is the most compressed representation of the IPv6 address 2001:0000:0000:abcd:0000:0000:0000:0001?
- 2001::abcd::1
- 2001:0:abcd::1
- 2001::abcd:0:1
- 2001:0:0:abcd::1 *
- 2001:0000:abcd::1
- What three application layer protocols are part of the TCP/IP protocol suite? (Choose three.)
- ARP
- DHCP *
- DNS *
- FTP *
- NAT
- PPP
- What are two features of ARP? (Choose two.)
- An ARP request is sent to all devices on the Ethernet LAN and contains the IP address of the destination host and its multicast MAC address.
- If no device responds to the ARP request, then the originating node will broadcast the data packet to all devices on the network segment.
- When a host is encapsulating a packet into a frame, it refers to the MAC address table to determine the mapping of IP addresses to MAC addresses.
- If a host is ready to send a packet to a local destination device and it has the IP address but not the MAC address of the destination, it generates an ARP broadcast.
- If a device receiving an ARP request has the destination IPv4 address, it responds with an ARP reply.
- In NAT translation for internal hosts, what address would be used by external users to reach internal hosts?
- outside global
- outside local
- inside local
- inside global
- The exhibit shows a network topology. PC1 and PC2 are connected to the Fa0/1 and Fa0/2 ports of the SW1 switch, respectively. SW1 is connected through its Fa0/3 port to the Fa0/0 interface of the RT1 router. RT1 is connected through its Fa0/1 to the Fa0/2 port of SW2 switch. SW2 is connected through its Fa0/1 port to the PC3.
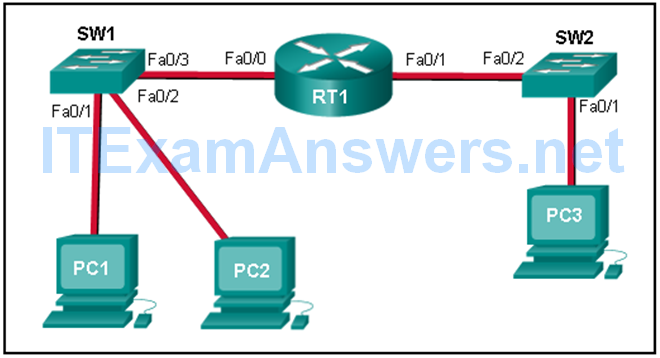
Refer to the exhibit. PC1 issues an ARP request because it needs to send a packet to PC2. In this scenario, what will happen next?
- SW1 will send an ARP reply with the PC2 MAC address.
- PC2 will send an ARP reply with its MAC address.
- RT1 will send an ARP reply with its Fa0/0 MAC address.
- RT1 will send an ARP reply with the PC2 MAC address.
- SW1 will send an ARP reply with its Fa0/1 MAC address.
- Which two characteristics are associated with UDP sessions? (Choose two.)
- Unacknowledged data packets are retransmitted.
- Destination devices receive traffic with minimal delay.
- Destination devices reassemble messages and pass them to an application.
- Transmitted data segments are tracked.
- Received data is unacknowledged.
- Refer to the exhibit. What is the global IPv6 address of the host in uncompressed format?
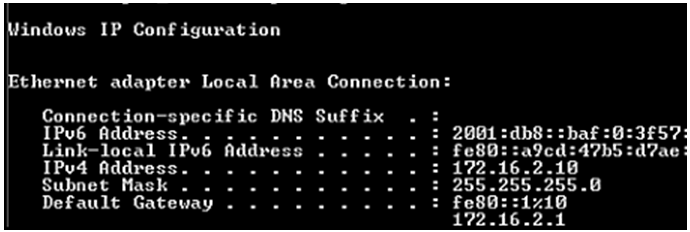
- 2001:0DB8:0000:0000:0BAF:0000:3F57:FE94
- 2001:0DB8:0000:0BAF:0000:0000:3F57:FE94
- 2001:DB80:0000:0000:BAF0:0000:3F57:FE94
- 2001:0DB8:0000:0000:0000:0BAF:3F57:FE94
- What is the purpose of the routing process?
- to provide secure Internet file transfer
- to convert a URL name into an IP address
- to forward traffic on the basis of MAC addresses
- to encapsulate data that is used to communicate across a network
- to select the paths that are used to direct traffic to destination networks
- What is the purpose of ICMP messages?
- to provide feedback of IP packet transmissions
- to monitor the process of a domain name to IP address resolution
- to inform routers about network topology changes
- to ensure the delivery of an IP packet
- What happens if part of an FTP message is not delivered to the destination?
- The message is lost because FTP does not use a reliable delivery method.
- The part of the FTP message that was lost is re-sent.
- The FTP source host sends a query to the destination host.
- The entire FTP message is re-sent.
- What is the primary purpose of NAT?
- conserve IPv4 addresses
- allow peer-to-peer file sharing
- enhance network performance
- increase network security
- Why does a Layer 3 device perform the ANDing process on a destination IP address and subnet mask?
- to identify the network address of the destination network
- to identify the host address of the destination host
- to identify the broadcast address of the destination network
- to identify faulty frames
- Refer to the exhibit. Using the network in the exhibit, what would be the default gateway address for host A in the 192.133.219.0 network?
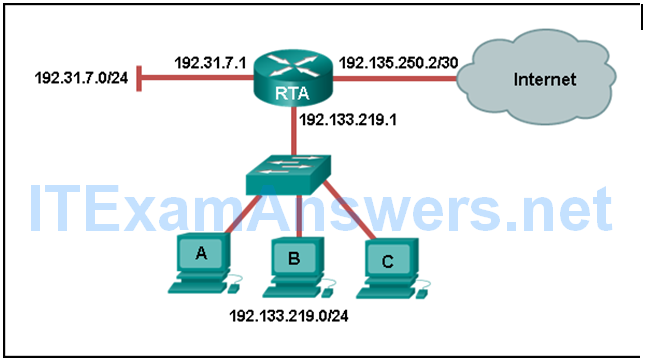
- 192.135.250.1
- 192.133.219.0
- 192.133.219.1
- 192.31.7.1
- Which three IP addresses are private ? (Choose three.)
- 192.167.10.10
- 10.1.1.1
- 192.168.5.5
- 172.16.4.4
- 172.32.5.2
- 224.6.6.6
