More Questions: Modules 1 – 4: Securing Networks Group Exam Answers
1. Which two statements describe access attacks? (Choose two.)
- Password attacks can be implemented by the use of brute-force attack methods, Trojan horses, or packet sniffers.
- Trust exploitation attacks often involve the use of a laptop to act as a rogue access point to capture and copy all network traffic in a public location, such as a wireless hotspot.
- Buffer overflow attacks write data beyond the allocated buffer memory to overwrite valid data or to exploit systems to execute malicious code.
- To detect listening services, port scanning attacks scan a range of TCP or UDP port numbers on a host.
- Port redirection attacks use a network adapter card in promiscuous mode to capture all network packets that are sent across a LAN.
- password – a dictionary is used for repeated login attempts
- trust exploitation – uses granted privileges to access unauthorized material
- port redirection – uses a compromised internal host to pass traffic through a firewall
- man-in-the-middle – an unauthorized device positioned between two legitimate devices in order to redirect or capture traffic
- buffer overflow – too much data sent to a memory location that already contains data
2. A user receives a phone call from a person who claims to represent IT services and then asks that user for confirmation of username and password for auditing purposes. Which security threat does this phone call represent?
- anonymous keylogging
- DDoS
- spam
- social engineering
3. What is the motivation of a white hat attacker?
- fine tuning network devices to improve their performance and efficiency
- taking advantage of any vulnerability for illegal personal gain
- studying operating systems of various platforms to develop a new system
- discovering weaknesses of networks and systems to improve the security level of these systems
4. A company has several sales offices distributed within a city. Each sales office has a SOHO network. What are two security features that are commonly found in such a network configuration? (Choose two.)
- biometric verifications
- WPA2
- Virtual Security Gateway within Cisco Nexus switches
- Cisco ASA firewall
- port security on user facing ports
5. Which security measure is best used to limit the success of a reconnaissance attack from within a campus area network?
- Implement restrictions on the use of ICMP echo-reply messages.
- Implement a firewall at the edge of the network.
- Implement access lists on the border router.
- Implement encryption for sensitive traffic.
6. What are two data protection functions provided by MDM? (Choose two.)
- remote wiping
- PIN locking
- inoculation
- quarantine
- physical security
7. Which condition describes the potential threat created by Instant On in a data center?
- when the primary firewall in the data center crashes
- when an attacker hijacks a VM hypervisor and then launches attacks against other devices in the data center
- when the primary IPS appliance is malfunctioning
- when a VM that may have outdated security policies is brought online after a long period of inactivity.
8. What functional area of the Cisco Network Foundation Protection framework is responsible for device-generated packets required for network operation, such as ARP message exchanges and routing advertisements?
- data plane
- control plane
- management plane
- forwarding plane
Control plane: Responsible for routing functions. Consists of the traffic generated by network devices to operate the network.
Management plane: Responsible for managing network devices.
Data (Forwarding) plane: Responsible for forwarding user data.
9. A security service company is conducting an audit in several risk areas within a major corporation. What statement describes the risk of using social networking?
- sensitive data lost through access to the cloud that has been compromised due to weak security settings
- gaining illegal access to corporate data by stealing passwords or cracking weak passwords
- data loss through access to personal or corporate instant messaging and social media sites
- the retrieval of confidential or personal information from a lost or stolen device that was not configured to use encryption software
10. What are two evasion methods used by hackers? (Choose two.)
- scanning
- access attack
- resource exhaustion
- phishing
- encryption
Resource exhaustion – keep the host device too busy to detect the invasion
Traffic fragmentation – split the malware into multiple packets
Protocol-level misinterpretation – sneak by the firewall
Pivot – use a compromised network device to attempt access to another device
Rootkit – allow the hacker to avoid detection as well as hide software installed by the hacker
11. Which attack involves threat actors positioning themselves between a source and destination with the intent of transparently monitoring, capturing, and controlling the communication?
- man-in-the-middle attack
- SYN flood attack
- DoS attack
- ICMP attack
12. A security service company is conducting an audit in several risk areas within a major corporation. What statement describes the risk of access to removable media?
- the potential of causing great damage because of direct access to the building and its infrastructure devices
- intercepted emails that reveal confidential corporate or personal information
- the unauthorized transfer of data containing valuable corporate information to a USB drive
- data loss through access to personal or corporate instant messaging and social media sites
13. What is the purpose of a reconnaissance attack on a computer network?
- to gather information about the target network and system
- to redirect data traffic so that it can be monitored
- to prevent users from accessing network resources
- to steal data from the network servers
This item is based on information contained in the presentation.
Preventing users from accessing network resources is a denial of service attack. Being able to steal data from the network servers may be the objective after a reconnaissance attack gathers information about the target network and system. Redirecting data traffic so it can be monitored is a man-in-the middle attack.
14. A security service company is conducting an audit in several risk areas within a major corporation. What statement describes an internal threat?
- data loss through access to personal or corporate instant messaging and social media sites
- the unauthorized transfer of data containing valuable corporate information to a USB drive
- the potential of causing great damage because of direct access to the building and its infrastructure devices
- gaining illegal access to corporate data by stealing passwords or cracking weak passwords
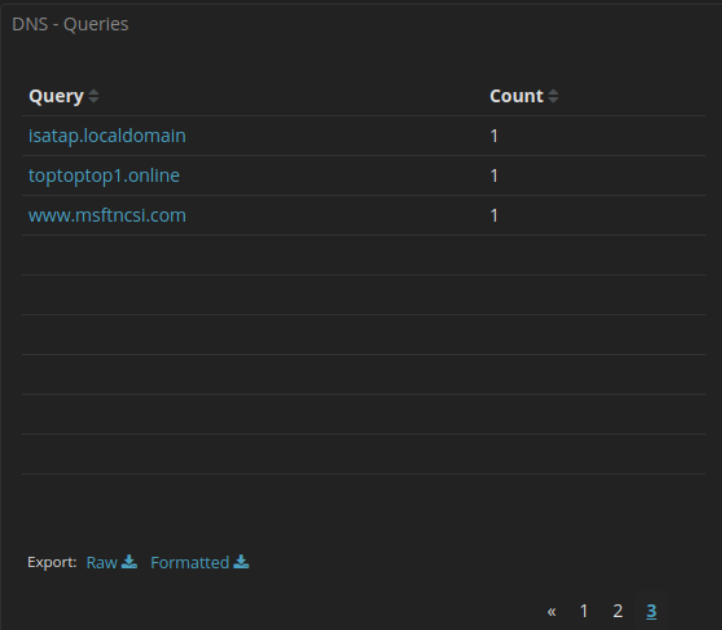
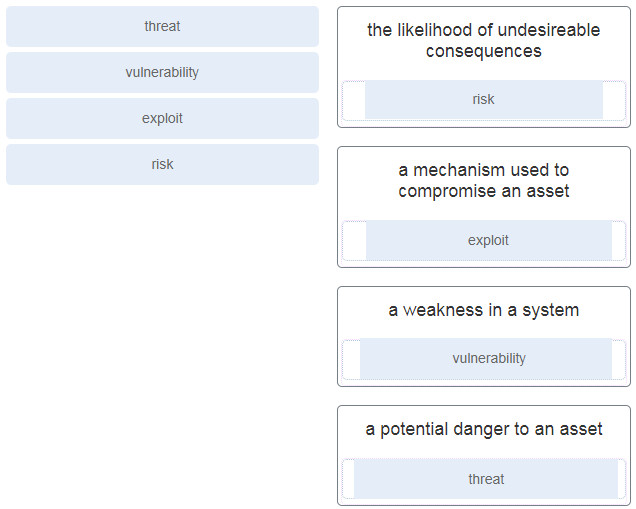
15. Match the security concept to the description.
16. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
- Configure DNS on the router.
- Configure the IP domain name on the router.
- Generate two-way pre-shared keys.
- Configure a host name other than “Router”.
- Enable inbound vty Telnet sessions.
- Generate crypto keys.
Step 1: Configure a hostname.
Step 2: Configure a domain name.
Step 3: Generate crypto keys.
17. Which command will block login attempts on RouterA for a period of 30 seconds if there are 2 failed login attempts within 10 seconds?
- RouterA(config)# login block-for 10 attempts 2 within 30
- RouterA(config)# login block-for 30 attempts 2 within 10
- RouterA(config)# login block-for 2 attempts 30 within 10
- RouterA(config)# login block-for 30 attempts 10 within 2
18. Which two practices are associated with securing the features and performance of router operating systems? (Choose two.)
- Install a UPS.
- Keep a secure copy of router operating system images.
- Configure the router with the maximum amount of memory possible.
- Disable default router services that are not necessary.
- Reduce the number of ports that can be used to access the router.
19. Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.)
- VTY interface
- console interface
- Ethernet interface
- boot IOS mode
- privileged EXEC mode
- router configuration mode
20. A network administrator enters the service password-encryption command into the configuration mode of a router. What does this command accomplish?
- This command encrypts passwords as they are transmitted across serial WAN links.
- This command prevents someone from viewing the running configuration passwords.
- This command enables a strong encryption algorithm for the enable secret password command.
- This command automatically encrypts passwords in configuration files that are currently stored in NVRAM.
- This command provides an exclusive encrypted password for external service personnel who are required to do router maintenance.
21. On which two interfaces or ports can security be improved by configuring executive timeouts? (Choose two.)
- Fast Ethernet interfaces
- console ports
- serial interfaces
- vty ports
- loopback interfaces
22. A security service company is conducting an audit in several risk areas within a major corporation. What statement describes an attack vector?
- data loss through access to personal or corporate instant messaging and social media sites
- the path by which a threat actor can gain access to a server, host, or network
- intercepted emails that reveal confidential corporate or personal information
- the unauthorized transfer of data containing valuable corporate information to a USB drive
23. A user is curious about how someone might know a computer has been infected with malware. What are two common malware behaviors? (Choose two.)
- The computer emits a hissing sound every time the pencil sharpener is used.
- The computer beeps once during the boot process.
- The computer gets increasingly slower to respond.
- No sound emits when an audio CD is played.
- The computer freezes and requires reboots.
Appearance of files, applications, or desktop icons
Security tools such as antivirus software or firewalls turned off or changed
System crashes
Emails spontaneously sent to others
Modified or missing files
Slow system or browser response
Unfamiliar processes or services running
Unknown TCP or UDP ports open
Connections made to unknown remote devices
24. Which security feature or device would more likely be used within a CAN than a SOHO or data center?
- security trap
- ESA/WSA
- virtual security gateway
- wireless router
- exit sensors
25. What is the purpose of mobile device management (MDM) software?
- It is used to create a security policy.
- It is used to implement security policies, setting, and software configurations on mobile devices.
- It is used to identify potential mobile device vulnerabilities.
- It is used by threat actors to penetrate the system.
26. Which security implementation will provide management plane protection for a network device?
- antispoofing
- routing protocol authentication
- role-based access control
- access control lists
27. A security service company is conducting an audit in several risk areas within a major corporation. What statement describes the risk of access to cloud storage devices?
- intercepted emails that reveal confidential corporate or personal information
- gaining illegal access to corporate data by stealing passwords or cracking weak passwords
- sensitive data lost through access to the cloud that has been compromised due to weak security settings
- the retrieval of confidential or personal information from a lost or stolen device that was not configured to use encryption software