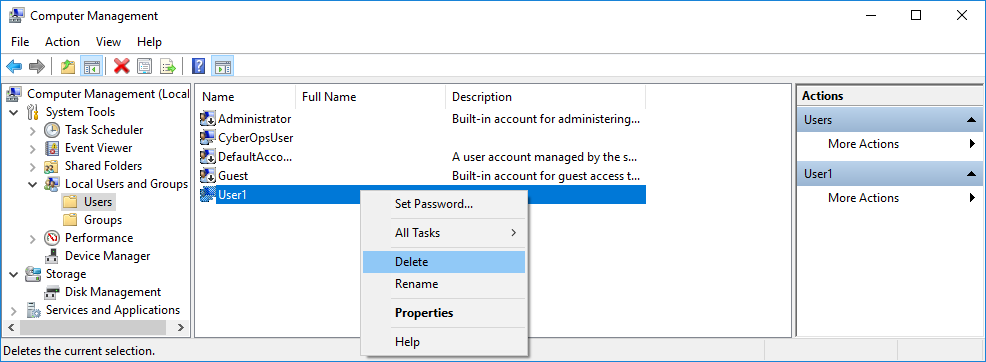
3.3.10 Lab – Create User Accounts (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Introduction…
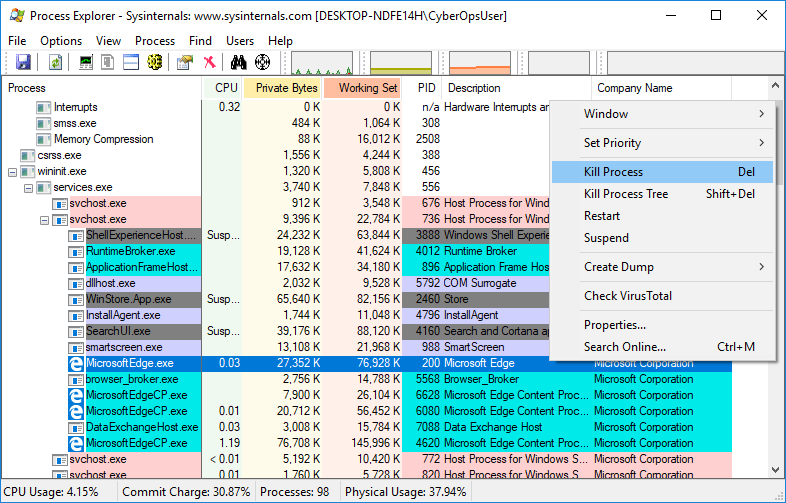
3.2.11 Lab – Exploring Processes, Threads, Handles, and Windows Registry (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the…
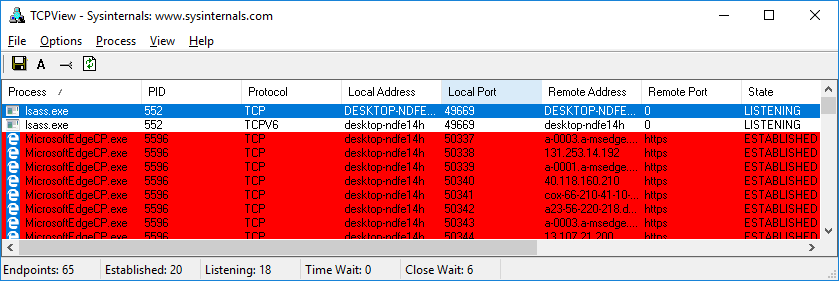
3.0.3 Class Activity – Identify Running Processes (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only.…
2.2.5 Lab – Becoming a Defender (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives…
1.3.4 Lab – Visualizing the Black Hats (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only.…
1.1.6 Lab – Cybersecurity Case Studies (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only. Objectives…
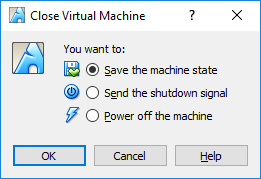
1.1.5 Lab – Installing the Virtual Machines (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy only.…
1.0.6 Class Activity – Top Hacker Shows Us How It is Done (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears…
1.2.3 Lab – Learning the Details of Attacks (Instructor Version) Instructor Note: Red font color or gray highlights indicate text that appears in the instructor copy…