Objectives Research and analyze cyber security incidents Background / Scenario Governments, businesses, and individual users are increasingly the targets of cyberattacks and experts predict that these attacks are likely to increase in the future. Cybersecurity education is a top international priority as high-profile cyber-security related incidents raise the fear that attacks could threaten the global economy. The Center for Strategic and International Studies estimates that the cost of cybercrime to the global economy is more than $400 billion annually and in the United State alone as many as 3000 companies had their systems compromised in 2013. In this lab you…
Author: CCNA Security
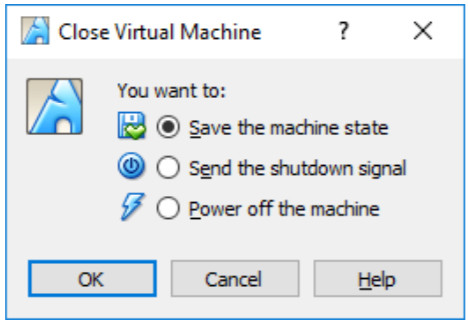
Objectives Part 1: Prepare a Personal Computer for Virtualization Part 2: Import a Virtual Machine into VirtualBox Inventory Background / Scenario Computing power and resources have increased tremendously over the last 10 years. A benefit of having multicore processors and large amounts of RAM is the ability to use virtualization. With virtualization, one or more virtual computers operate inside one physical computer. Virtual computers that run within physical computers are called virtual machines. Virtual machines are often called guests, and physical computers are often called hosts. Anyone with a modern computer and operating system can run virtual machines. A virtual…
A technician notices that an application is not responding to commands and that the computer seems to respond slowly when applications are opened. What is the best administrative tool to force the release of system resources from the unresponsive application? Event Viewer System Restore Add or Remove Programs Task Manager Which three technologies should be included in a security information and event management system in a SOC? (Choose three.) firewall appliance threat intelligence VPN connection security monitoring vulnerability tracking intrusion prevention In which situation is an asymmetric key algorithm used? An office manager encrypts confidential files before saving them to…
What is the responsibility of the human resources department when handing a security incident as defined by NIST? Review the incident policies, plans, and procedures for local or federal guideline violations. Perform disciplinary actions if an incident is caused by an employee. Coordinate the incident response with other stakeholders and minimize the damage of an incident. Perform actions to minimize the effectiveness of the attack and preserve evidence. What is the responsibility of the IT support group when handing an incident as defined by NIST? reviews the incident policies, plans, and procedures for local or federal guideline violations performs actions…
What are three functions provided by the syslog service? (Choose three.) to provide statistics on packets that are flowing through a Cisco device to select the type of logging information that is captured to specify the destinations of captured messages to periodically poll agents for data to gather logging information for monitoring and troubleshooting to provide traffic analysis Which method can be used to harden a device? Allow users to re-use old passwords. Force periodic password changes. Allow USB auto-detection. Allow default services to remain enabled. Refer to the exhibit. Which field in the Sguil event window indicates the number…
What is a chain of custody? The documentation surrounding the preservation of evidence related to an incident * A list of all of the stakeholders that were exploited by an attacker The disciplinary measures an organization may perform if an incident is caused by an employee A plan ensuring that each party involved in an incident response understands how to collect evidence What type of CSIRT organization is responsible for determining trends to help predict and provide warning of future security incidents? Analysis center * Vendor team Coordination center National CSIRT Which approach can help block potential malware delivery methods,…
Which term describes evidence that is in its original state? Corroborating evidence Best evidence * Indirect evidence Direct evidence How is the hash value of files useful in network security investigations? It helps identify malware signatures. It is used to decode files. It is used as a key for encryption. It verifies confidentiality of files. Which tool is a Security Onion integrated host-based intrusion detection system? OSSEC Sguil ELSA Snort Which type of evidence supports an assertion based on previously obtained evidence? direct evidence corroborating evidence best evidence indirect evidence Which tool is developed by Cisco and provides an interactive…
Which Windows tool can be used to review host logs? Services Event Viewer * Task Manager Device Manager Which two protocols may devices use in the application process that sends email? (Choose two.) HTTP SMTP * POP IMAP DNS * POP3 How does using HTTPS complicate network security monitoring? HTTPS cannot protect visitors to a company-provided web site. HTTPS can be used to infiltrate DNS queries. Web browser traffic is directed to infected servers. HTTPS adds complexity to captured packets. . Which protocol is used to send e-mail messages between two servers that are in different e-mail domains? POP3 SMTP…
Which class of metric in the CVSS Basic metric group defines the features ofthe exploit such as the vector, complexity, and user interaction required by the exploit? Impact Exploitability * Modified Base Exploit Code Maturity Which step in the Vulnerability Management Life Cycle performs inventory of all assets across the network and identifies host details, including operating system and open services? Assess Discover * Remediate Prioritize assets In network security assessments, which type of test is used to evaluate the risk posed by vulnerabilities to a specific organization, including assessment of the likelihood of attacks and the impact of successful…