Objectives Research and analyze what it takes to become a network defender Background / Scenario In our technology-centric world, as the world gets more connected, it…
Browsing: CCNA CyberOps Associate
- Modules 1 – 2: Threat Actors and Defenders Group Exam (Answers)
- Modules 3 – 4: Operating System Overview Group Exam (Answers)
- Modules 5 – 10: Network Fundamentals Group Exam (Answers)
- Modules 11 – 12: Network Infrastructure Security Group Exam (Answers)
- Modules 13 – 17: Threats and Attacks Group Exam (Answers)
- Modules 18 – 20: Network Defense Group Exam (Answers)
- Modules 21 – 23: Cryptography and Endpoint Protection Group Exam (Answers)
- Modules 24 – 25: Protocols and Log Files Group Exam (Answers)
- Modules 26 – 28: Analyzing Security Data Group Exam (Answers)
- CA Skills Assessment Exam
- Practice Final Exam (Answers)
- FINAL EXAM (Answers)
- Certification Practice Exam (Answers)
Objectives Research and analyze cyber security incidents Background / Scenario In 2016, it was estimated that businesses lost $400 million dollars annually to cyber criminals. Governments,…
Objectives Research and analyze IoT application vulnerabilities Background / Scenario The Internet of Things (IoT) consists of digitally connected devices that are connecting every aspect of…
Objectives Research and analyze cyber security incidents Background / Scenario Governments, businesses, and individual users are increasingly the targets of cyberattacks and experts predict that these…
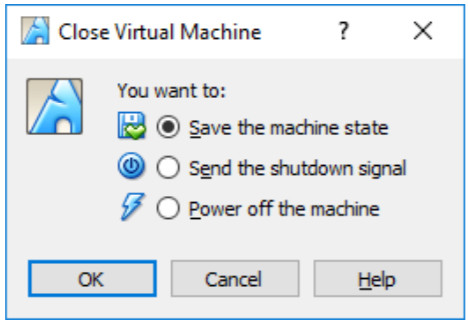
Objectives Part 1: Prepare a Personal Computer for Virtualization Part 2: Import a Virtual Machine into VirtualBox Inventory Background / Scenario Computing power and resources have…
A technician notices that an application is not responding to commands and that the computer seems to respond slowly when applications are opened. What is the…
What is the responsibility of the human resources department when handing a security incident as defined by NIST? Review the incident policies, plans, and procedures for…
What are three functions provided by the syslog service? (Choose three.) to provide statistics on packets that are flowing through a Cisco device to select the…
What is a chain of custody? The documentation surrounding the preservation of evidence related to an incident * A list of all of the stakeholders that…