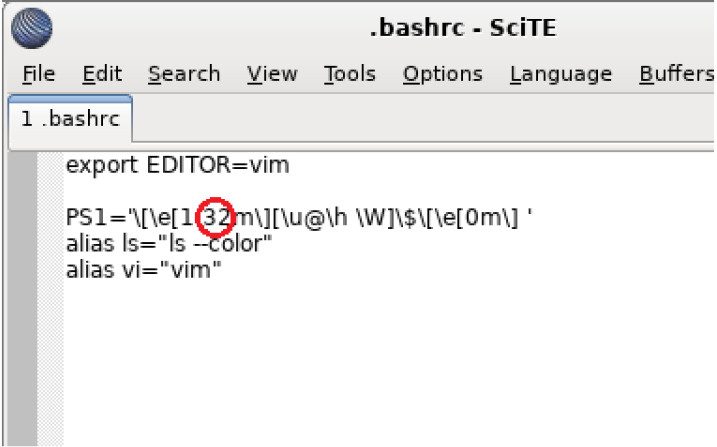
Introduction In this lab, you will get familiar with Linux command line text editors and configuration files. Required Resources CyberOps Workstation Virtual Machine Part 1: Graphical…
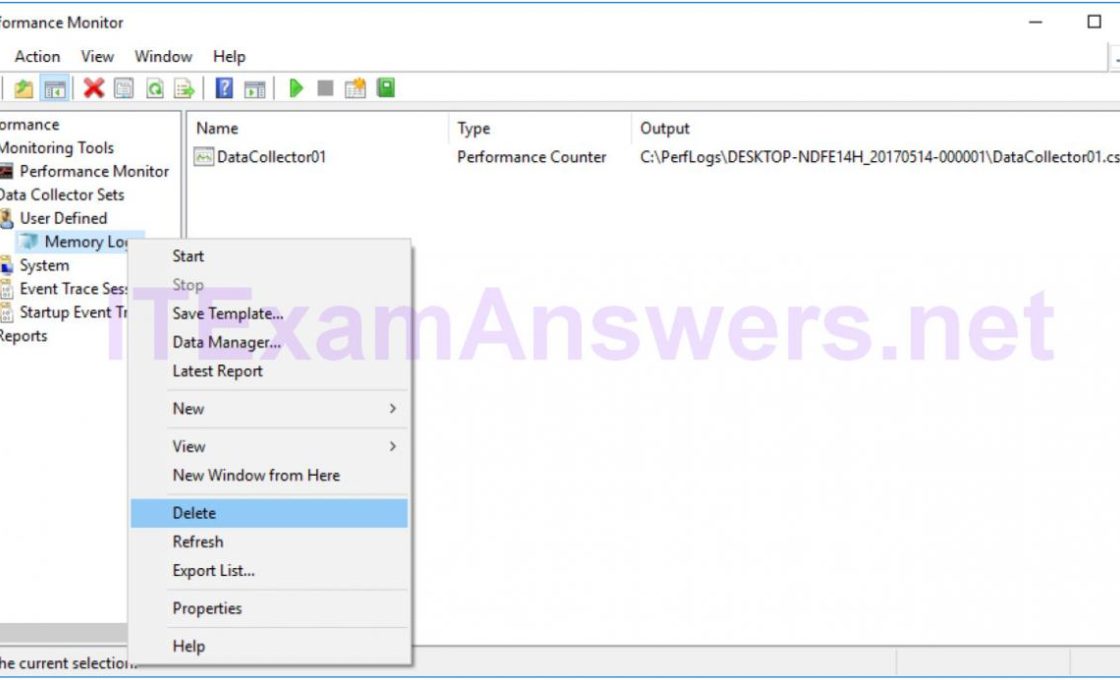
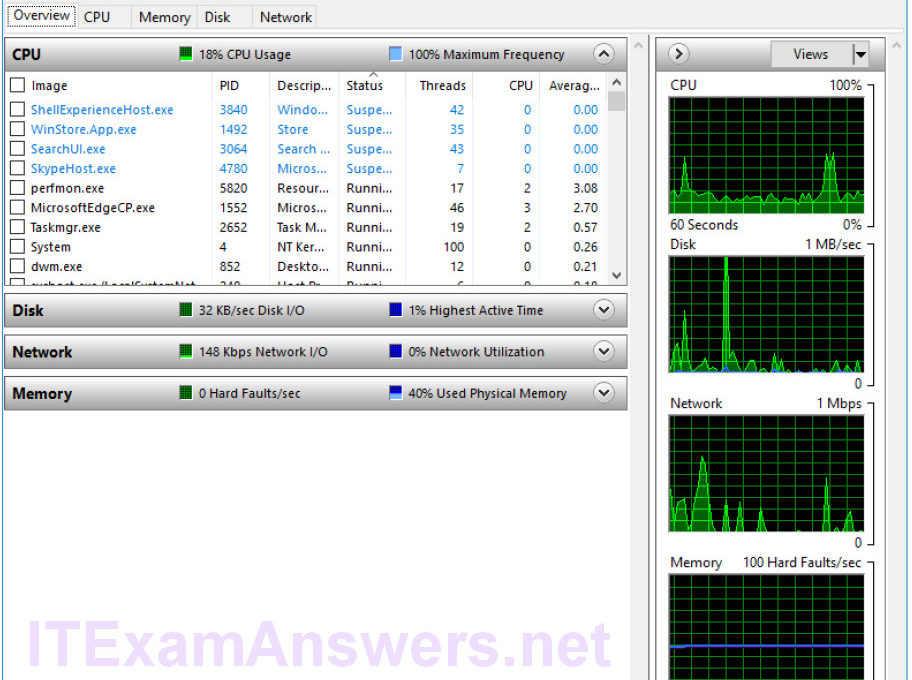
Introduction In this lab, you will use administrative tools to monitor and manage Windows system resources. Recommended Equipment A Windows PC with Internet access Part 1:…
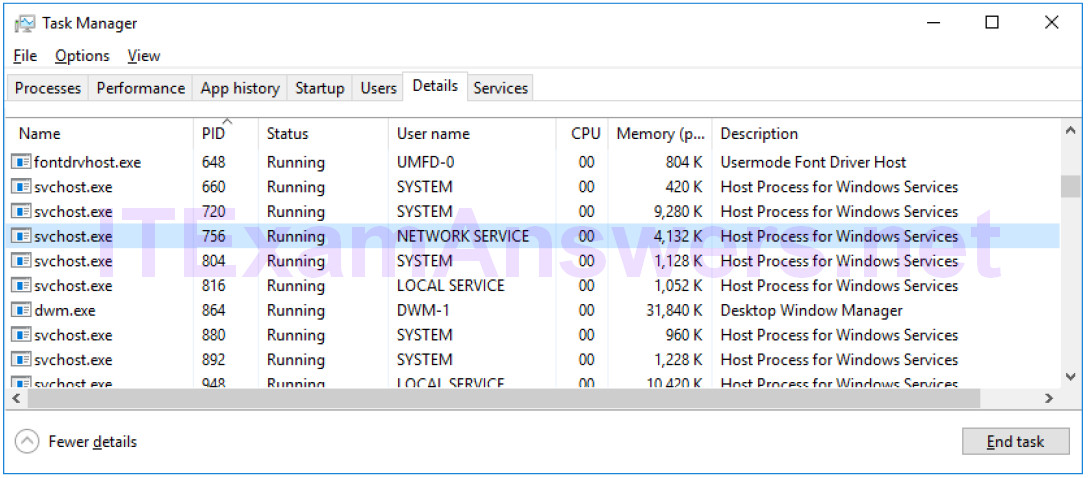
Introduction In this lab, you will explore Task Manager and manage processes from within Task Manager. Part 1: Working in the Processes tab Part 2: Working…
Objectives The objective of the lab is to explore some of the functions of PowerShell. Background / Scenario PowerShell is a powerful automation tool. It is…
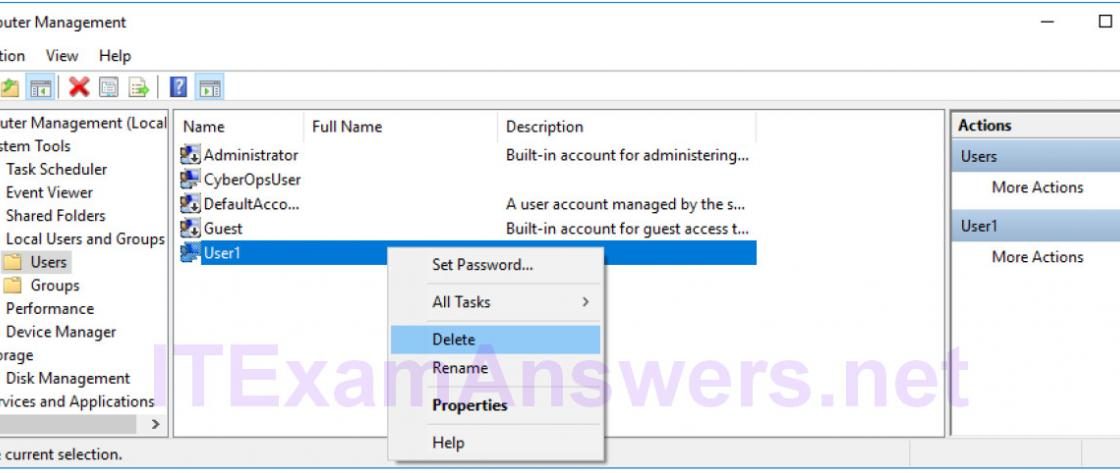
Introduction In this lab, you will create and modify user accounts in Windows. Part 1: Creating a New Local User Account Part 2: Reviewing User Account…
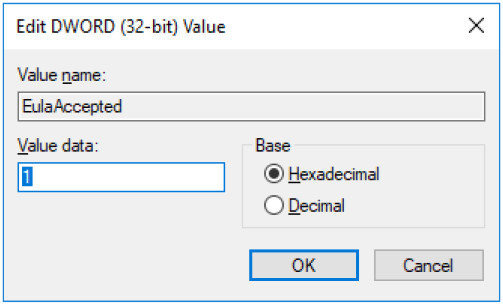
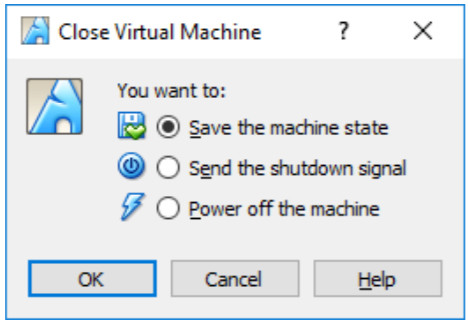
Objectives In this lab, you will explore the processes, threads, and handles using Process Explorer in the SysInternals Suite. You will also use the Windows Registry…
Objectives Research and analyze what it takes to become a network defender Background / Scenario In our technology-centric world, as the world gets more connected, it…
Objectives Research and analyze cyber security incidents Background / Scenario In 2016, it was estimated that businesses lost $400 million dollars annually to cyber criminals. Governments,…
Objectives Research and analyze IoT application vulnerabilities Background / Scenario The Internet of Things (IoT) consists of digitally connected devices that are connecting every aspect of…